Ease of IVR menu flow configuration and editing.
Legacy IVR systems can require developer assets to be used from the IVR payments partner when initially configuring a menu and IVR workflow and subsequent edits should the menu flow require a change. In many cases these can be extremely expensive to the using organization. We have heard instances where a using organization was quoted thousands of dollars to change from using a text to speech engine to using their own recorded voice talent. It should have be be as such.
Some modern IVR payment systems allow the using organization access to a user interface that provides them the ability to change any attributes within the workflow and menu system on their own, without the need for development  resources being used. This amounts to the elimination of what would have been substantial costs. In relation to the changing from text to speech engine to using recorded voice talent, it can be as simple as dragging and dropping a wav file into the user interface.
resources being used. This amounts to the elimination of what would have been substantial costs. In relation to the changing from text to speech engine to using recorded voice talent, it can be as simple as dragging and dropping a wav file into the user interface.
Multiple Payment Options
Many organizations having the need for IVR payments already have a credit card processor. The ability for an IVR system to utilize multiple card processors is key to adoption. While some processors might require an API integration, typically a gateway already integrated to the IVR system can connect to the existing card processor, enabling the using organization a fast setup for acceptance of payments via the IVR system.
Additionally, many organizations have the need for accepting ACH payments via the IVR system. Having that option can result in much lower processing costs versus credit card transactions. Having an ACH option available and ready to go with the IVR system can be advantageous for many using organizations.
IVR systems can function in both an inbound call and outbound call scenario. Inbound IVR payment calls are typically pretty straight forward in that at some point during the call the customer or donor is prompted to enter their credit card or bank account information in order to remit a payment. Outbound IVR calls have the 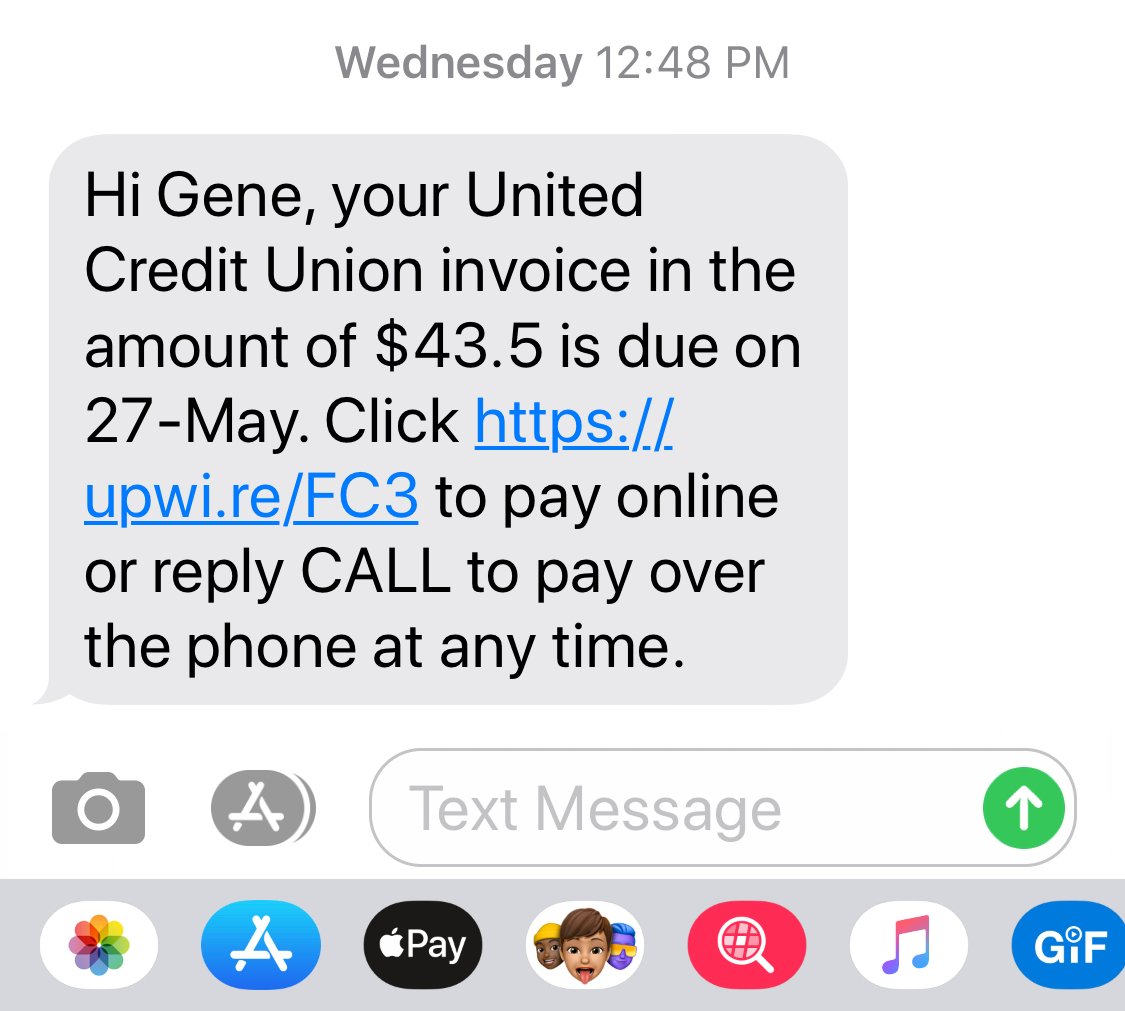 potential to utilize a method different than entering card data over an IVR phone call. Customers receiving an outbound IVR call can have the ability to initiate an outbound SMS message to be delivered to their phone that contains a link that can render a payment page on their mobile device where payment information can be entered and remitted. This provides an additional option that serves towards reducing security concerns.
potential to utilize a method different than entering card data over an IVR phone call. Customers receiving an outbound IVR call can have the ability to initiate an outbound SMS message to be delivered to their phone that contains a link that can render a payment page on their mobile device where payment information can be entered and remitted. This provides an additional option that serves towards reducing security concerns.
Data Security
The most important aspect of security surrounding IVR payments is the sensitive data; credit card and bank account data. This data must be handled securely in a PCI compliant system. There are multiple ways to secure sensitive data, but one that stands out as it relates to IVR systems is to utilize what is known as Zero Knowledge Architecture (ZKA). IVR systems that employ ZKA never record or store sensitive data. An IVR system to uses ZKA, even if it were to be compromised, can’t provide the hacker what it doesn’t have. There’s nothing stored to be stolen. A ZKA IVR system exceeds PCI compliance standards.
Of course there’s other data that might be presented during an IVR call such as account numbers, names and amounts due. While these aren’t typically sensitive, those data points shouldn’t be available to being compromised. Two methods of data population exist for modern IVR systems; API integration and secure upload to cloud storage. In either case the data is stored and called from a PCI compliant system and method.
If your organization has a need for IVR payments, reach out and contact us. We’ll listen to all your requirements and present solutions that we think will work best for you and your organization.



